What is Cyber Threat Hunting?
Cyber threat hunting is the active security search of networks, endpoints, and data sets to hunt for malicious, suspicious, or risky activity that has escaped detection by existing tools. So there is a difference between cyber threat detection and cyber threat hunting. Threat detection is a somewhat passive approach to monitoring data and systems for potential security issues, but it’s still a necessity and can help a threat hunter. Proactive cyber threat detection tactics have evolved to use previously collected data with new threat intelligence to identify and categorize potential threats before an attack.
Security personnel cannot afford to believe that their security system is impenetrable. They must remain alert for another threat or vulnerability. Rather than sitting back and waiting for threats to strike, cyber threat hunting builds hypotheses based on knowledge of the behavior of threat actors and validates those hypotheses through active searches of the environment. With threat hunting, the expert does not start with an alert or even indicators of compromise (TOC), but with deeper reasoning and forensics. In most cases, the hunter’s efforts create and justify an alert or IOC. Cyber threat hunting aggressively assumes that a breach has occurred or will occur within a company. Security guards are hunting for threats in their environment, not using the latest tool.
Threat hunting research
Traditional cyber threat hunting is based on a manual process where a security analyst examines data based on their knowledge of the network and systems to make assumptions about potential threats. Cyber threat hunting has achieved efficiency and effectiveness with the addition of automation, machine learning, and User and Entity Behavior Analytics (UEBA) to alert enterprise security teams to potential risks.
Once the risk or potential risk is identified, as well as the frequency of hunting, an investigation is initiated. Examples of cyber threat hunting research include:
- Hypothesis-Driven Investigations: Upon discovery of significant information about a new, imminent threat vector, cyber threat hunting will delve into network or system logs to look for hidden anomalies or trends that could signal a new threat. Analytics-driven research: Search-driven information gathered using machine learning (ML) and artificial intelligence (AI) tools.
- Study of Tactics, Techniques and Procedures (TTP): Hunting for attack manners generally uses the same operational methods. This is useful for obtaining or assigning a threat and using existing remediation methods that worked with this behavior.
Threat hunting is specific to each environment, but some techniques can be applied to almost any environment. The main threat hunting techniques include:
Base line
Baselining helps the hunter understand what “normal” looks like in an organization. SANS describes the value of grounding as looking for a needle in a haystack, removing hay by double-digit percentages to reduce the time it takes for the needle to become visible. To minimize the time needed to coordinate baseline analysis with the attacker’s technique, SANS suggests hunters consider the following questions:
- How common is PowerShell in your environment?
- If common, what does a typical sysadmin activity look like?
- Where does PowerShell activity typically come from and under which user accounts does it typically run?
As a result, a hunter may not need to root PowerShell in its entirety, but rather look for unexpected deviations or attacker-specific command structures.
Hunting for specific attacks
A baseline helps the hunter understand the overall hunting environment, but specific attack hunts can help track down malicious activity faster. Specific attack hunts typically focus on a specific threat actor or threat. However, the limits of their particular hunting pattern can throw off false positives. Offensive hunts combined with base lining often produce good results.
Time sensitivity
All hunts are time sensitive, so hunters must periodically confirm their baselines. SANS recommends confirming that the installation of new software does not introduce unnecessary traffic that results in false positives. To keep up with attackers switching to new methods or reverting to old methods, hunters must validate intelligence-driven hunts and even re-hunt if outdated techniques are detected.
Third Party Sources
Hunting for needles in a data haystack can overwhelm hunting teams. Third-party providers can help hunters hunt more successfully. SANS lists the following benefits that hunters can collect from third-party sources:
- Rejecting false positive leads
- Focus on interesting leads
- IP address lookups
- Geographical location
- Encrypted stream metadata
- Log detection
- Overlays of the attacker’s technique
- Analysis of links between internal and external or host and network data points
Five steps to threat hunting
Cyber threat hunting consists of steps or processes to hunt effectively and successfully. These steps include:
Step 1: Hypothesis
Threat hunting begins with a hypothesis or statement about the hunter’s ideas about what threats might be in the environment and how to find them. A hypothesis may include the tactics, techniques and procedures (TPP) of the suspected attacker. Threat hunters use threat intelligence, environmental knowledge, and their experience and creativity to create a logical path to detection.
Step 2: Collect and process insights and data
Threat hunting requires quality intelligence and data. A plan for data collection, centralization and processing is required. Security information and event management (SIEM) software can provide insights and operational results in an enterprise’s IT environment.
Step 3: Trigger
A hypothesis can act as a trigger where advanced detection tools direct threat hunters to initiate an investigation of a particular system or specific area of the network.
Step 4: Research
Probe technology can hunt or search deep into potentially malicious system or network anomalies, ultimately found to be benign or confirmed as malicious.
Step 5: Response/Decision
Data collected from confirmed malicious activity can be fed into automated security technology to respond, resolve and mitigate threats. Actions can include removing malware files, restoring modified or deleted files, updating firewall/IPS rules, applying security patches, and changing system configurations — all while better understanding what happened and how to improve your security against similar future attacks.
Threat Hunting Maturity Model
A company’s cyber threat hunting maturity model is defined by the quantity and quality of data an organization collects from its IT environment. A company’s cyber threat hunting capabilities for hunting and responding, toolsets and analytics factor into its threat hunting maturity model. The SANS Institute defines the Threat Hunting Maturity Model as:
- Initial: A maturity level 0 organization relies primarily on automated reporting and performs little or no routine data collection.
- Minimum: At maturity level 1, the organization includes threat intelligence indicator searches. It has a medium to high level of routine data collection.
Procedural: At Level 2 maturity, the organization follows analytical procedures developed by others. It has a high or very high level of routine data collection. - Innovative: In maturity level 3, the organization creates new data analysis procedures. It has a high or very high level of routine data collection.
- Leading: At Level 4 maturity, the organization automates most of its successful data analysis procedures. It has a high or very high level of routine data collection.).
The benefits of automation in cyber threat hunting
Today’s adversaries are automating their methods, tactics, and procedures to circumvent preemptive defenses, so it makes sense that enterprise security teams can better keep up with attacks by automating their manual workload. Incorporating automation benefits cyber threat detection processes and helps SOCs make better use of their staff and resources. That includes:
- Datasets: Cyber threat research involves collecting data from many categories and sources, requiring many hours to manually sort and separate the good data from the bad data. Automation can greatly reduce the time required for assembly and increase valuable security SOC resources.
- Investigation Process: The seemingly constant volume of threat alerts and alerts can overwhelm even the most experienced and well-functioning SOC. Automation can cut through the threat noise by quickly categorizing threats as high, medium, and low risk, reducing security staff time and allowing them to effectively respond to those that require immediate action or further investigation.
- Prevention Process: Once a threat is identified, risk mitigation measures must be put in place across enterprise networks, endpoints and the cloud.
- Response process: Automated responses can counter smaller, more common attacks, such as executing a custom script to isolate a compromised endpoint, deleting malicious files after isolation, and automatically using backup information to restore data compromised during an attack.
What does it take to hunt cyber threats?
What basic security resources does an enterprise need to enable threat hunting or a threat hunting service?
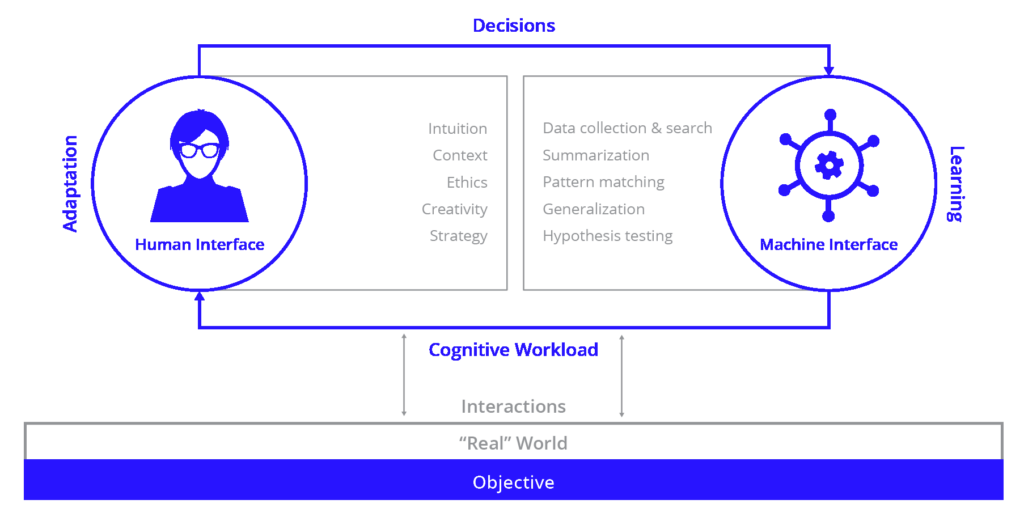
Optimize the human experience with a team of human machines
Never expect machines to be ethical or strategic. Never expect people to know how to search large amounts of data quickly and at scale or do complex pattern matching.
Human Hunters: Effective and efficient cyber threat detection programs budget staff and analyst time to focus on the hunt. Threat hunting requires human interaction and input to reach a solution faster and more accurately. Knowledge of the threat landscape and a solid understanding of the IT landscape, as well as creative and intuitive thinking, are the fundamentals of a cyber threat hunter. People help solve the problem faster and more accurately, eliminate unnecessary and mundane manual errors that can be riddled with errors.
Organizational Model: Each organization must choose the most appropriate organizational model for its hunting team. The models are based on the size and budget of the organization, as well as the availability of analysts with various skills. According to SANS: “Threat hunting involves a more mature organization with a defensive network architecture, advanced incident response capabilities and a security monitoring/security operations team.”
Tools and Technologies: Many companies use comprehensive endpoint security solutions for detection, response and investigation, security monitoring and management tools often used by threat hunters. These solutions may include:
SIEM and statistical intelligence analysis tools like SAS programs
Threat Intelligence Service Providers (TIPS) and/or industry threat databases. This extends to other elements such as the FSIAC (Financial Services Information Sharing and Analysis Center) for security data with actionable metrics.
Bad IP Address or Hash, Vulnerability Management of Published Risks, and Trusted Online Threat Publications.
Generally speaking, these technologies are isolated and require a cyber threat hunter to manually sift through the value to reach a conclusive conclusion. This can be daunting for organizations without human expertise.
Data: After establishing a baseline of network traffic or system behavior, a baseline of expected and allowable events can be created against which anomalies can be identified. Use threat analysis first to focus on high-impact malicious activity.